3D Solutions
CHROMOS Industrial begleitet Unternehmungen mit einer einmaligen Kombination aus Produkten und Dienstleistungen auf dem Weg zum wirkungsvollen und gewinnbringenden Einsatz von additiven Fertigungsmethoden. Mit unserer Expertise und innovativen Technologien stehen wir als starker Partner an Ihrer Seite, um die Vorteile der digitalen Fertigung voll auszuschöpfen.
Das vielseitige Angebot von CHROMOS 3D Solutions
Entdecken Sie das transformative Potenzial unseres 3D Solutions-Angebots für verschiedenste Branchen. Mit einem umfassenden Spektrum an Technologien und Services unterstützen wir Sie vom Prototyping bis zur Endproduktion. Nutzen Sie unsere Expertise, um Ihre Produktentwicklungszyklen zu verkürzen, die Effizienz zu steigern und innovative Lösungen schneller auf den Markt zu bringen.
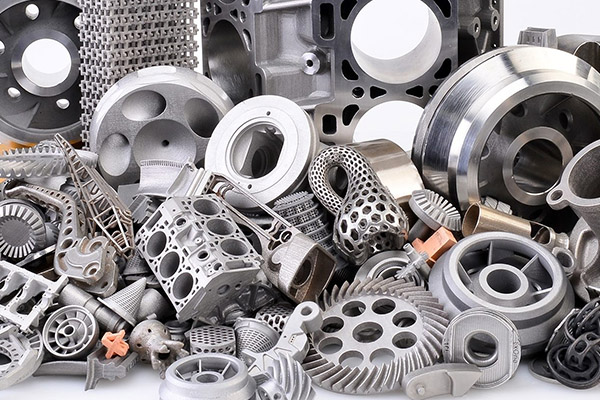
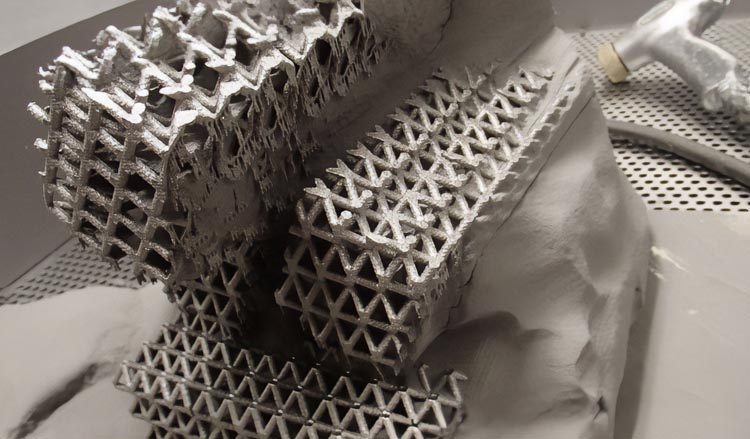
Revolutionäre 3D-Technologien
- Breites Spektrum an 3D Druck- technologien und Materialien, von Kunststoffen, über Beton bis Metall, angepasst an die Bedürfnisse der Industrie.
- Rennomierte Partner: Sika, Desktop Metal, Yizumi, BigRep, Sinterit und mehr
- 3D-Scanning & CAD: Für Reverse Engineering und sonstige Projekte

Umfassende Dienstleistungen
- Individuelle Beratung für die Implementierung von 3D-Drucklösungen in bestehende Produktionsprozesse
- Professioneller 3D-Druck- und Scanservice, von Prototyping bis zur Endfertigung
- Wartung und technischer Support, um eine optimale Leistung der 3D-Drucksysteme zu gewährleisten

Bildung und Wissensaustausch
- Workshops, Seminare und Zertifizierungskurse zu neuesten 3D-Drucktechnologien und -anwendungen
- Kooperationen mit Universitäten und Forschungsinstituten zur Weiterentwicklung der additiven Fertigung
- Regelmässige Community-Veranstaltungen
SERVICE
Schnell, präzise, zuverlässig
Ein effektiver technischer Service ist für uns als Bindeglied zwischen Herstellern und Kunden unerlässlich, besonders bei technischen Investitionsgütern. Seit über 75 Jahren bieten wir umfassende technische Betreuung in Branchen wie der grafischen und Verpackungsindustrie, Lebensmittel- und Getränkeproduktion, Pharmazie sowie für verarbeitende Industrien, Labore und Bildungs- sowie Forschungseinrichtungen.
Unsere 40 qualifizierten Servicetechniker leisten Reparaturen, Wartungen, Präventivservice, Projektierung, Neumontagen, Schulungen, Umzüge und Inbetriebnahmen sowie Ersatzteilbeschaffung.
PARTNER
Erstklassige Produkte für individuelle Lösungen
Die meisten unserer Beziehungen zu Partnern bestehen bereits seit langem und gründen auf grossem Vertrauen sowie hoher Kompetenz beider Seiten. Dadurch können wir unseren Kunden qualitativ hochwertige Produkte anbieten, hergestellt von Unternehmen, denen wir vollständig vertrauen. Unser umfangreiches Portfolio an Partnern ermöglicht es uns, unseren Kunden nicht nur einzelne Produkte, sondern eine massgeschneiderte Produktkonstellation anzubieten. Egal wie originell oder spezifisch Ihre Wünsche oder Anforderungen sind, wir haben die passenden Produkte für Ihr Anliegen.
Bei CHROMOS Industrial sind Sie an der richtigen Adresse
Jahrzehntelange Erfahrung
Wir sind ein etabliertes Schweizer Unternehmen mit jahrzehntelanger Erfahrung im Vertrieb komplexer Investitionsgüter. Unsere bewährte Fachkompetenz und unsere tiefgreifende Branchenkenntnis machen uns zu einem verlässlichen Partner für anspruchsvolle Herausforderungen im Bereich des industriellen 3D-Drucks.
Technologieführerschaft
Wir unterstützen Sie aktiv dabei, die richtige Technologie zu identifizieren, um bestehende Prozesse durch effizientere und kostensparende 3D-Workflows zu ersetzen. Unsere Fachexperten begleiten Sie durch den gesamten Prozess und helfen Ihnen, die optimale Lösung für Ihre Anforderungen zu finden und umzusetzen.
Umfassender Service
Unsere umfangreiche Serviceabteilung mit 40 Mitarbeitern steht Ihnen zur Verfügung, um sicherzustellen, dass unsere verkauften Systeme reibungslos funktionieren und maximale Leistung erzielen. Wir bieten schnellen technischen Support, regelmässige Wartungsdienste und Schulungen, um sicherzustellen, dass Sie das Beste aus Ihrer Investition herausholen können.
Kontakt
Unsere Experten helfen Ihnen gerne weiter. Kontaktieren Sie uns!